I’ve just come across a new issue where the latest release of Horizon fails to connect to the vCenter. The only error message you get is “Certificate validation failed”
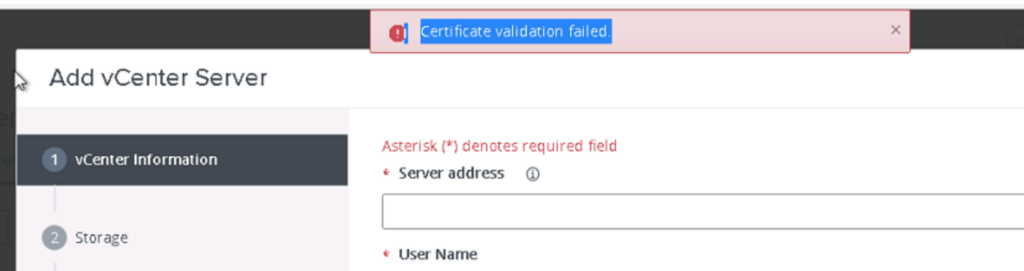
This problem is caused by Horizon dropping support for certificate signature algorithms including SHA512withRSA
Finding the cause of Certificate validation failed
To confirm this is the problem you are experiencing, lets check in the Connection Server debug log stored in the following location on your Connection Server:
C:\ProgramData\VMware\VDM\logs\ debug-[year]-[month]-[timestamp].txtFor confirmation that this is the issue you are facing, you are looking for the keyphrase “SSLHandshakeException” which shows that “Certificates do not conform to algorithm constraints.”
Caused by: javax.net.ssl.SSLHandshakeException: SSLHandshakeException invoking https://vcenter.vsphere.local:443/sdk: Certificates do not conform to algorithm constraintsNext we need to confirm which signature algorithm is being used by your vCenter’s certificate.
Caused by: java.security.cert.CertPathValidatorException: Algorithm constraints check failed on signature algorithm: SHA512withRSASo we can see that it is failing on signature algorithm SHA512withRSA.
To fix this we need to add these certificate signature algorithms to the override in the Horizon ADAM database.
You can find details about connecting to the ADAM Database on VMware KB2012377
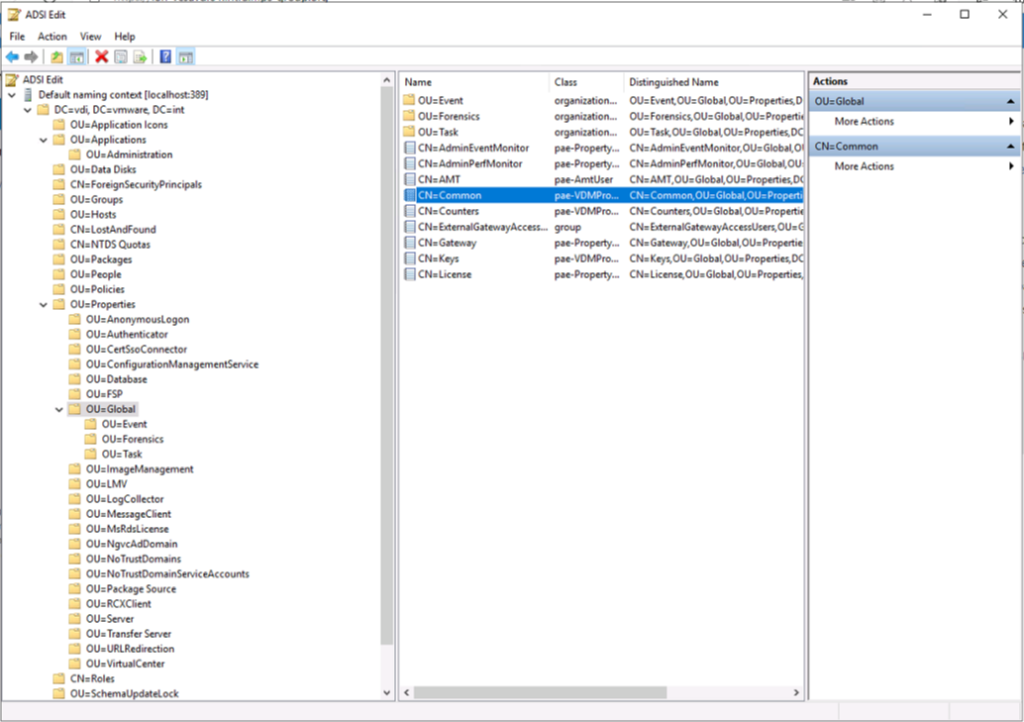
Connect to the Horizon ADAM Database
- Start the ADSI Edit utility on your Horizon Connection Server.
- In the console tree, select Connect to.
- In the Select or type a Distinguished Name or Naming Context text box, type the distinguished name
DC=vdi, DC=vmware, DC=int - In the Select or type a domain or server text box, select or type
localhost:389or the fully qualified domain name (FQDN) of the View Connection Server computer followed by port 389. - Click OK.
- Select and expand DC=vdi,dc=vmware,dc=int to expand.
- Go to
ou=propertiesthenou=globaland go to properties oncn=common
- Find the LDAP attribute
pae-SSLServerSignatureSchemesand add the following entry:\LIST:rsa_pkcs1_sha256,rsa_pkcs1_sha384,rsa_pkcs1_sha512,rsa_pss_rsae_sha512,rsa_pss_pss_sha512 - Find the LDAP attribute
pae-SSLClientSignatureSchemesand add the following entry:\LIST:rsa_pkcs1_sha256,rsa_pkcs1_sha384,rsa_pkcs1_sha512,rsa_pss_rsae_sha512,rsa_pss_pss_sha512- IMPORTANT: The new list must include at least rsa_pkcs1_sha256 and rsa_pkcs1_sha384 to avoid breaking other outgoing connections.

- Restart the Connection server service on all brokers in the cluster.
References
For reference, the default list of schemes is as follows:
rsa_pss_rsae_sha384
rsa_pss_rsae_sha256
rsa_pss_pss_sha384
rsa_pss_pss_sha256
rsa_pkcs1_sha384
rsa_pkcs1_sha256
If you require SHA1 you need to add
rsa_pkcs1_sha1,rsa_pss_rsae_sha1,rsa_pss_pss_sha1
If you require SHA512 you need to add
rsa_pkcs1_sha512,rsa_pss_rsae_sha512,rsa_pss_pss_sha512
VMware have also depreciated other protocols and ciphers in Horizon
The following protocols and ciphers are disabled by default:
- SSLv3
- TLSv1 and TLSv1.1
- RC4
NOTE: It is not possible to enable support for ECDSA certificates. These certificates have never been supported.
Further details of these are HERE